In the shadowed corridors of enterprise data vaults, where vast troves of sensitive information underpin decision-making, a quiet revolution stirs. GraphRAG, Microsoft's ingenious fusion of knowledge graphs and large language models, promises to unravel the narrative threads buried in private documents, delivering answers that are not just accurate but profoundly contextual. Yet, as enterprises grapple with zkML GraphRAG privacy imperatives, the raw power of this technology risks exposing personally identifiable information (PII) to unseen vulnerabilities. Drawing from my sixteen years in macro research, where zkML has fortified confidential long-term forecasts in bonds and global markets, I advocate for identity agnostic AI zkML as the cornerstone of trustworthy systems. By marrying GraphRAG with zero-knowledge machine learning and UUID-only knowledge graphs, organizations can achieve enterprise zkML PII protection without sacrificing analytical depth.
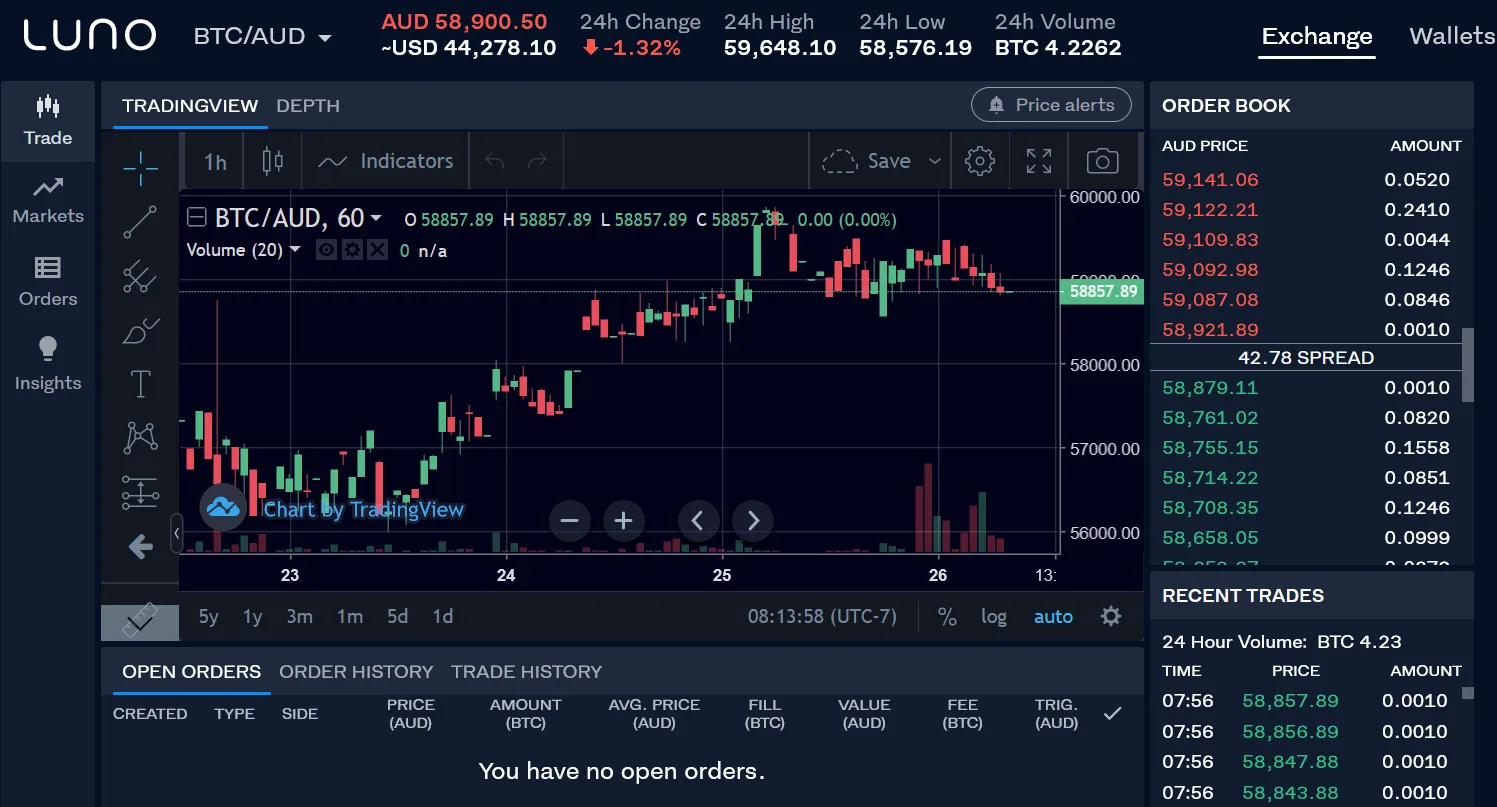
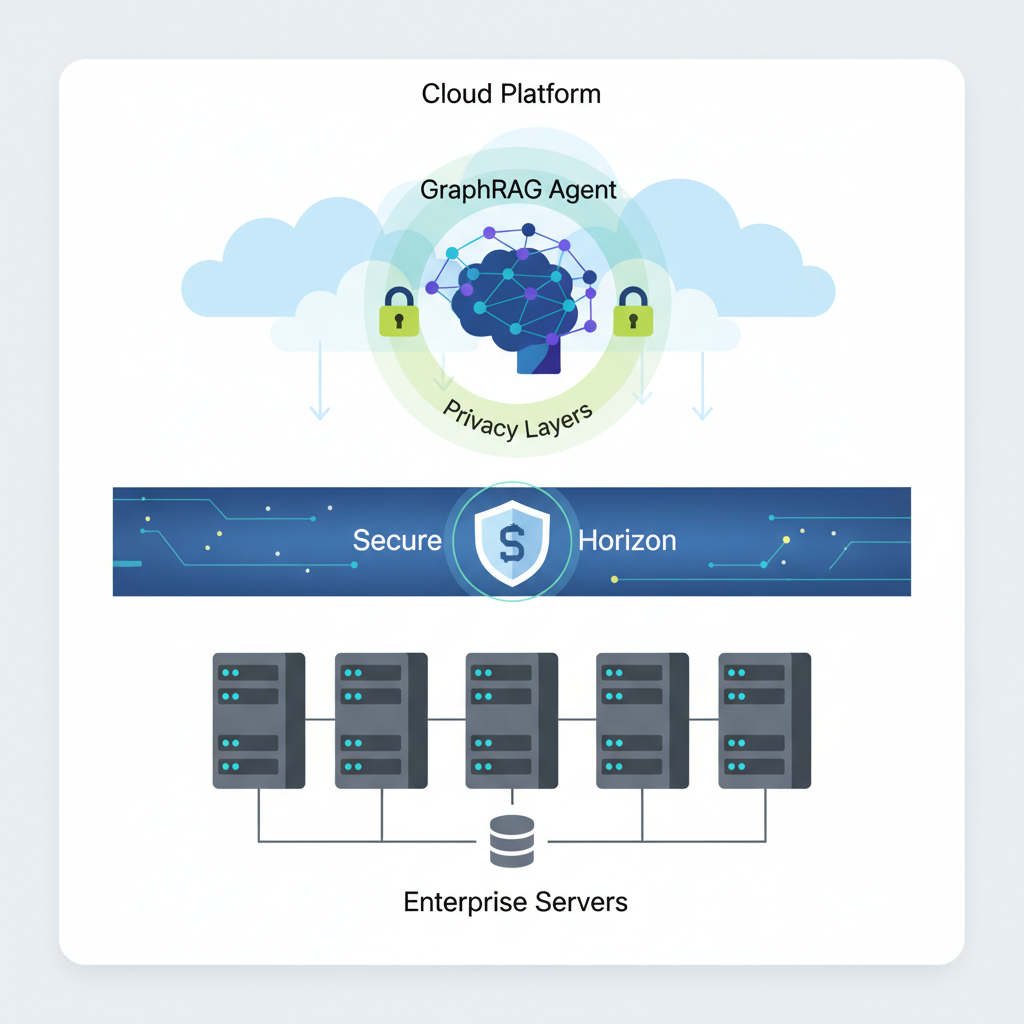
Consider the enterprise landscape: documents, PDFs, and wikis brim with unstructured knowledge that traditional retrieval-augmented generation (RAG) struggles to navigate. GraphRAG transforms this chaos into structured insight, leveraging LLM-generated graphs to boost question-answering performance on private data. Recent advancements, as highlighted in Graphwise's platform integration, position it as the trust layer for verifiable AI. In my conservative fundamental approach, this shift resonates deeply; it mirrors how zkML anonymizes model inferences in institutional analytics, ensuring low-risk narratives amid regulatory scrutiny.
GraphRAG's Leap Beyond Linear Retrieval
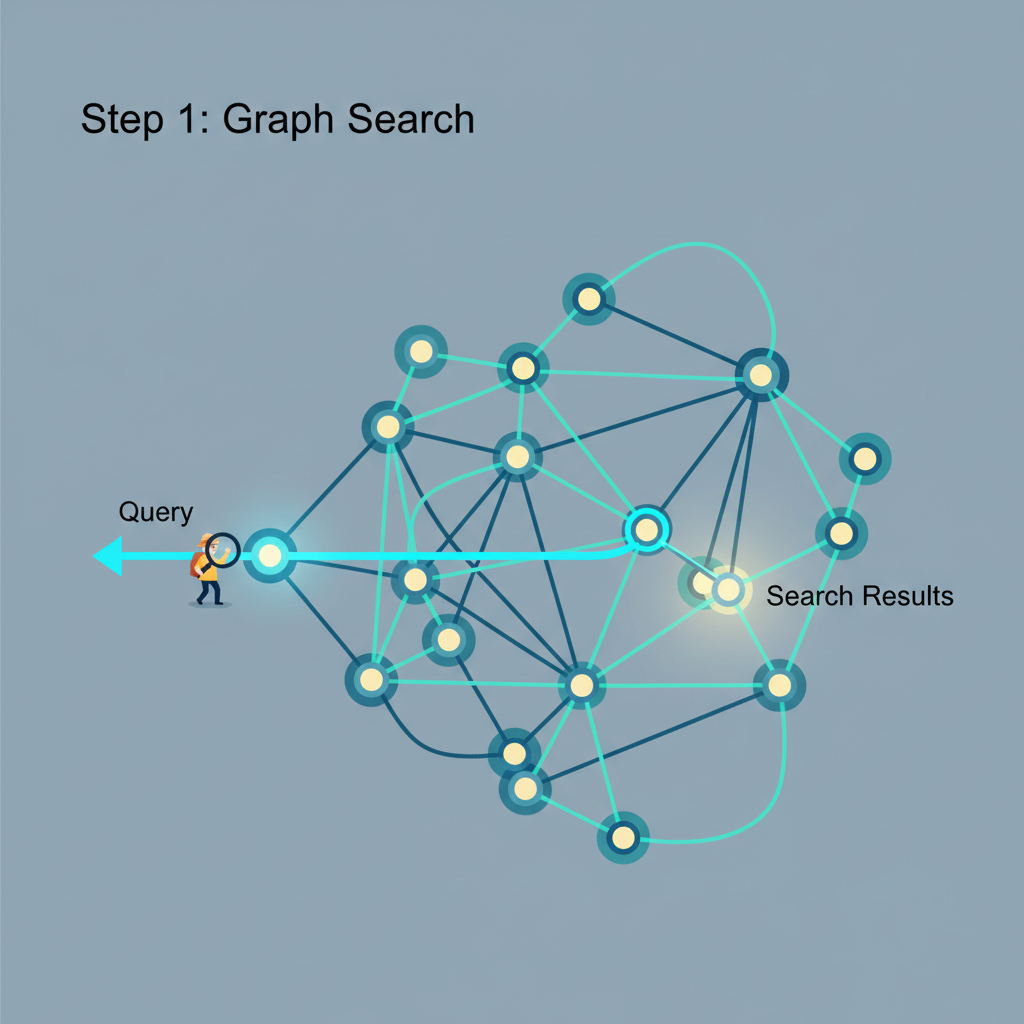
At its core, GraphRAG decouples the LLM from rote text search, instead constructing dynamic knowledge graphs that capture entities, relationships, and hierarchies. This enables discovery across narrative private data, where standard RAG falters on interconnected stories. Microsoft's research demonstrates substantial gains in recall and precision, particularly for complex queries demanding global context. For enterprises, this means AI agents that reason over wikis and reports with unprecedented fidelity, as showcased in AWS demonstrations of GraphRAG-powered agents.
Yet, herein lies the reflective pause: while GraphRAG unlocks LLM potential, its graphs often embed raw PII, inviting compliance pitfalls under GDPR or HIPAA. PersonaAgent frameworks on arXiv further personalize this power, but at what privacy cost? My experience in zkML applications whispers caution; without safeguards, even the most sophisticated graphs become liability vectors.
Identity-Agnostic Processing: UUIDs as Privacy Sentinels
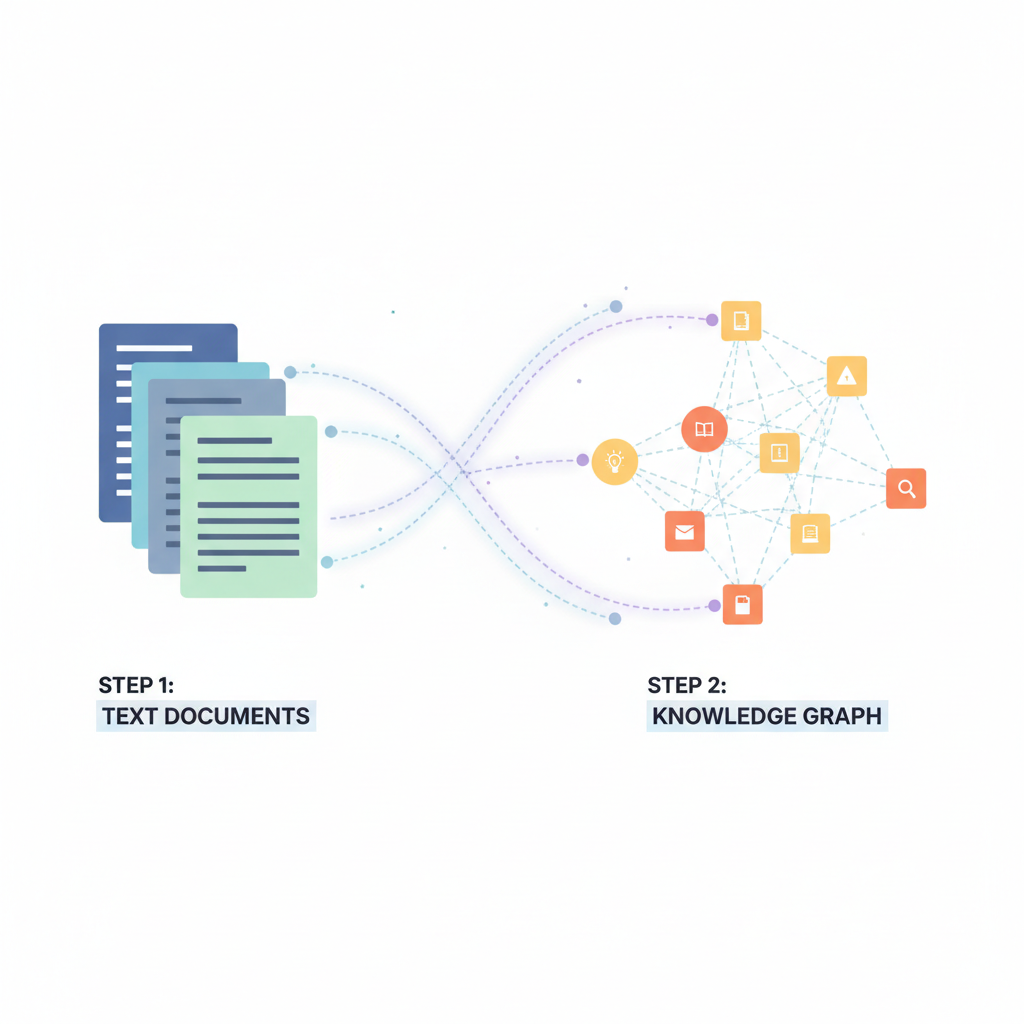
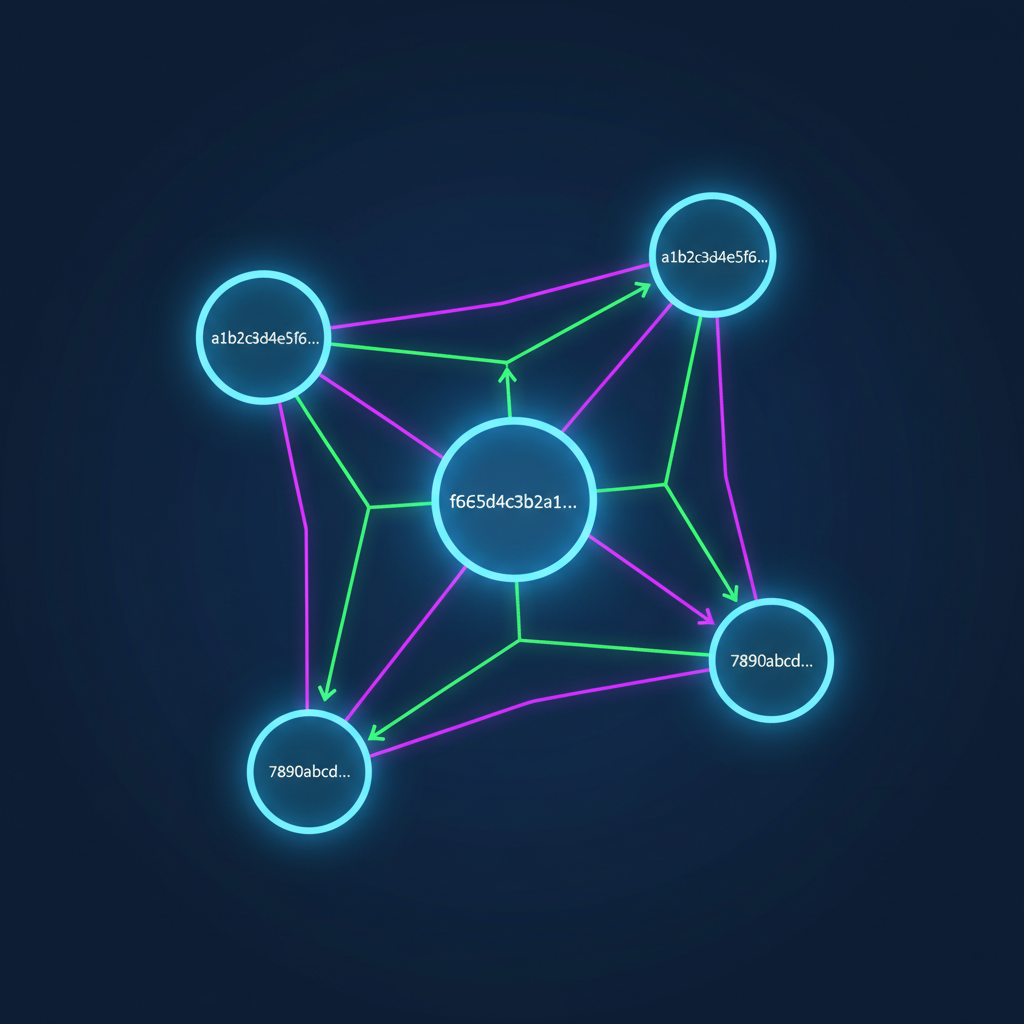
Enter identity-agnostic processing, a paradigm where knowledge graphs store only anonymized UUIDs, severing ties to sensitive identities. Thomas Rehmer's architecture articulates this eloquently: "Your identity data is protected by a privacy-first architecture. " Sensitive attributes reside in isolated vaults, referenced obliquely via tokens. This decoupling not only thwarts breaches but simplifies audits, allowing transparent claims of protection.
In practice, ingestion pipelines hash PII into UUIDs, populating graphs with edges like "UUID-A relates to UUID-B via transaction. " Queries resolve these dynamically against encrypted stores, preserving utility. For macro forecasters like myself, this echoes zkML's role in bonds analytics, where market signals inform models sans exposing proprietary positions. Enterprises adopting this mitigate hallucination risks too; Volodymyr Pavlyshyn notes GraphRAG's context quality varies, but UUID abstraction enforces disciplined retrieval.
zkML's Verifiable Veil Over Graph Computations
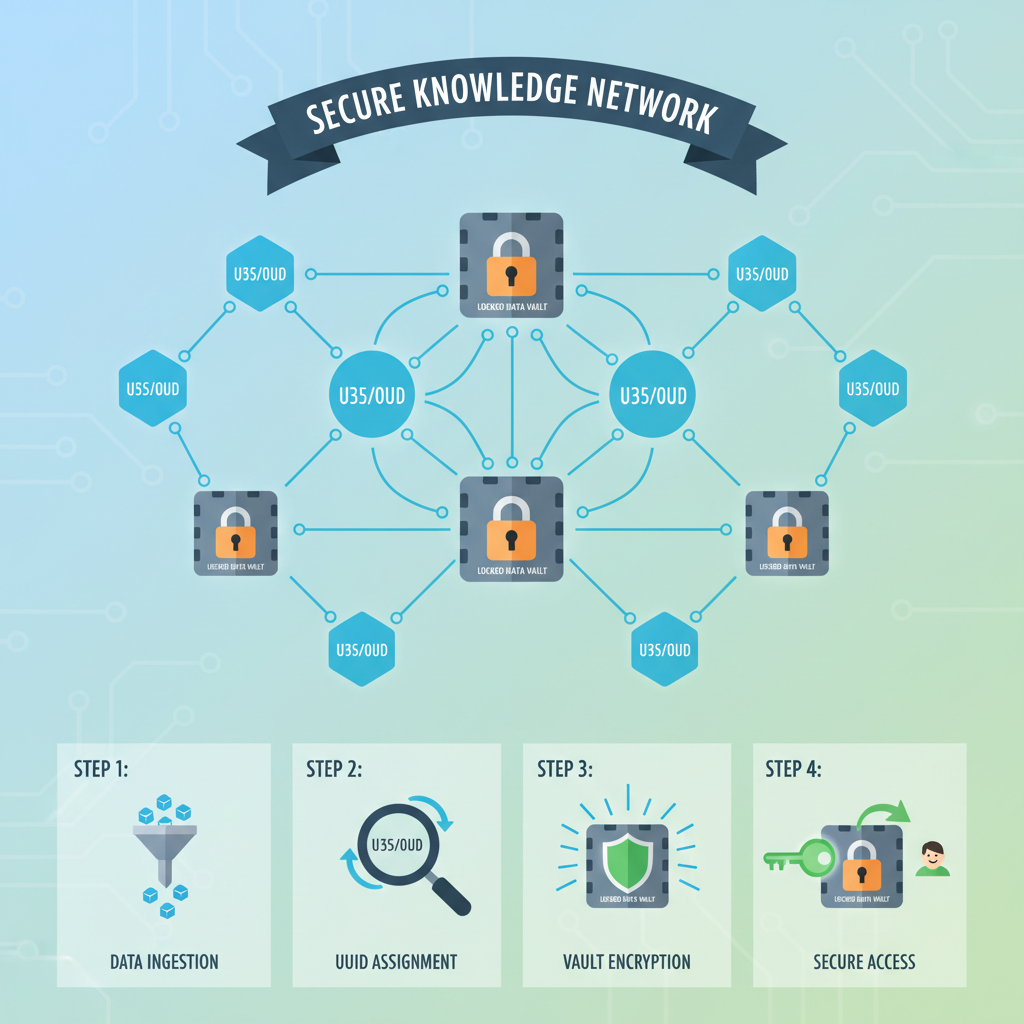
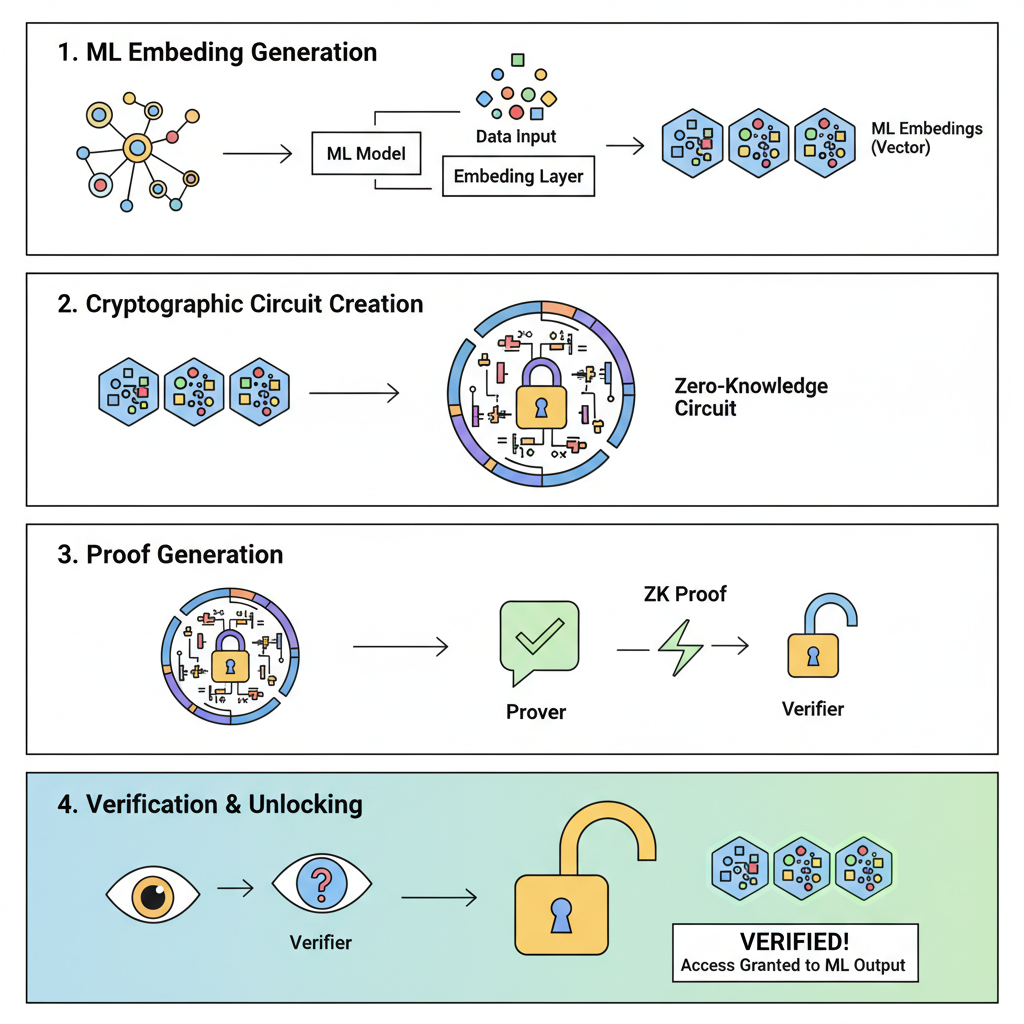
Zero-knowledge machine learning elevates this framework, proving computations on encrypted data without revelation. ZKTorch and similar tools compile ML models into zk circuits, enabling GraphRAG inferences on private graphs. Imagine traversing UUID-linked nodes, embedding them into LLMs, and generating responses; zkML attests correctness sans data exposure. Kudelski Security underscores its promise for transparent, fair AI, while ARPA highlights biometric privacy parallels, like iris verification.
World's Orb exemplifies on-device zkML for uniqueness proofs from biometrics, a blueprint for enterprise GraphRAG. In my view, this convergence crafts low-risk ecosystems; zkML ensures not just privacy but verifiability, countering RAG's variable quality with cryptographic rigor.
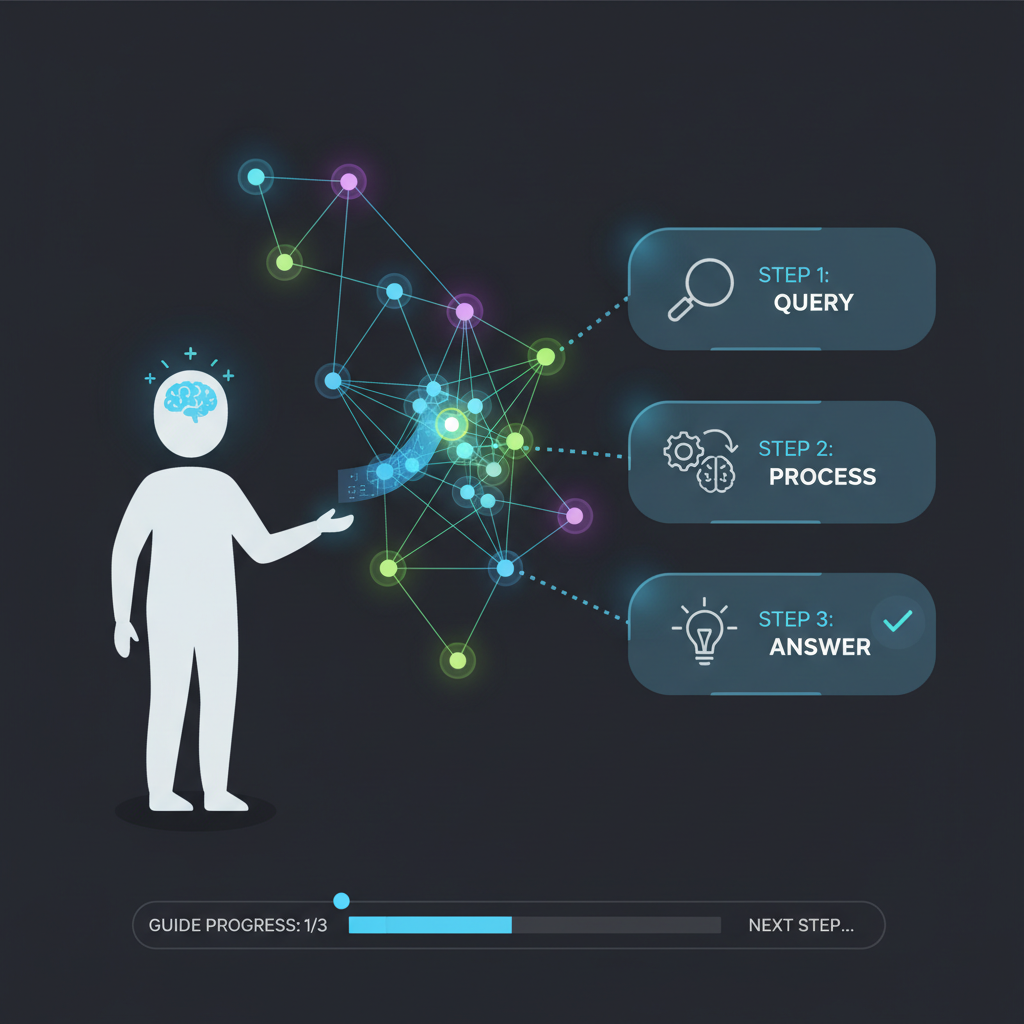
Integrating these layers demands architectural finesse, yet yields unparalleled resilience. Enterprises can now deploy GraphRAG agents that query UUID graphs, invoke zkML-proven embeddings, and synthesize responses grounded in private narratives. This triad addresses the core frailties of LLMs: opacity, leakage, and inconsistency. From my vantage in macro research, where zkML shields bond yield predictions from institutional eyes, such systems foster conservative confidence; decisions rest on verifiable insights, not shadowed assumptions.
Forging the Identity-Agnostic GraphRAG Pipeline
The pipeline begins with data ingestion, where PII extraction precedes hashing into UUIDs. Graphs bloom from these abstractions, capturing relational essence without nominative traces. During retrieval, GraphRAG communities aggregate UUID clusters relevant to queries; zkML circuits then prove vector similarities over encrypted embeddings. Generation follows, with LLMs conditioned on proven contexts, outputting answers laced with proof handles for audit trails.
This workflow, refined through tools like ZKTorch, scales to enterprise volumes. Microsoft's GraphRAG evolves here into a privacy fortress, where narrative discovery thrives amid regulatory tempests. PersonaAgent extensions gain zkML personae, personalizing sans profiling risks.
Reflecting on ZK13 discussions, compiling ML to zero-knowledge proofs remains computationally intensive, yet on-device precedents like World's Orb signal maturation. For global markets, I envision zkML GraphRAG forecasting trade flows from anonymized transaction webs, proving correlations without exposing counterparties. Such applications demand disciplined engineering; hasty UUID mappings risk collision vulnerabilities, underscoring my preference for conservative hashing namespaces.
Enterprise Safeguards: From Compliance to Competitive Edge
Beyond defense, this fusion confers advantage. Enterprises communicate credibly: "Our AI leverages privacy-by-architecture, proven via zkML. " Audits become effortless, as graphs reveal structure sans substance, and proofs certify integrity. In healthcare, UUID-linked patient narratives enable GraphRAG diagnostics compliant with HIPAA; finance unlocks fraud patterns from transaction UUIDs under GDPR. KPMG's privacy whitepapers affirm this alignment, positioning adopters ahead in trust economies.
Comparison of RAG vs GraphRAG vs zkML-GraphRAG
| Feature | RAG | GraphRAG | zkML-GraphRAG |
|---|---|---|---|
| Privacy | Low | Medium | High |
| Verifiability | None | Partial | Full |
| PII Risk | High | Medium | Zero |
| Enterprise Suitability | Limited | Good | Optimal |
Challenges persist: zk circuit latency challenges real-time queries, and LLM hallucinations linger despite enriched contexts. Pavlyshyn's critique rings true; quality contexts mitigate, not eradicate, fabrications. Yet zkML's verifiability imposes accountability, flagging anomalous proofs. My sixteen years counsel patience; as ZKTorch matures, latencies shrink, mirroring zkSNARK evolutions in blockchain.
Enterprises poised at this inflection wield GraphRAG with zkML identity-agnostic processing as a macro instrument, charting low-risk paths through data deluges. In bonds forecasting, it has transformed opaque signals into crystalline narratives; scaled enterprise-wide, it redefines AI stewardship. The shadowed corridors brighten, privacy intact, insights unbound.












No comments yet. Be the first to share your thoughts!